Bots Are Coming at APIs: How to Avoid API Bot Attacks?
22 Dec 2021 • 10 min read
Bots Are Coming at APIs: How to Avoid API Bot Attacks?
22 Dec 2021 • 10 min read
Gartner predicts that by 2022, API attacks will become the most-frequent attack vector. As bot technology evolves and APIs become popular among developers, bot attacks on APIs are growing, yet the use of bot management tools lags behind.
API: The Future of IT Infrastructure
APIs are everywhere. Almost every website application today has them. As more enterprises move to the cloud, they tend to share business capabilities with partners and bring in new services and technologies via application programming interfaces (APIs), which allows for quicker integration and faster deployment of new services.
APIs let one of your products or services communicate with other products and services easily without having to know how they’re implemented. Therefore, it enables enterprises to integrate applications and leverage existing technologies easily.
In this digital age we are living in, innovation is vital for the success of business and APIs are beneficial for companies in allowing them to become efficient and competitive in today's market.
Growing API Bot Attacks & The Importance of API Security
Now API threats are at a record high. The prevalent yet poorly protected APIs attract bad actors to exploit weakness in these connection points, such as login, online ordering, comment, and vote etc.
This has already drawn the attention of organizations and security vendors. According to the published data, there are three issues about API that should cause alarm for people.
- Poorly protected
Around 40% of organizations surveyed reported that more than one-half of their applications are exposed to the internet or third-party services via APIs, while nearly 66% of enterprises don't have a proper security measure for their APIs.
- Growing attacks
Attacks targeting APIs are increasing at an alarming rate - up 348% in six months by the third quarter of 2021, reported by Salt Labs.
- Hidden risk
Gartner predicts that by 2022, API attacks will become the most-frequent attack vector, causing data breaches for enterprise web applications.
Due to the popularity of cost-effective and time-saving APIs, API currently account for 83% of all Internet traffic, while HTML traffic has fallen to 17%, citing data from Akamai. While APIs become the foundation of business digital transformation, they also increase chances for malicious actors to access business data at the same time. Once malicious bots take advantage of sensitive data that they extract from APIs, enterprises may suffer significant financial loss or reputational damage.
Key Bot Attacks on APIs
API bot attacks could affect enterprises from all sectors. Technology, financial service, healthcare, and entertainment companies are widely viewed as at the forefront of API use - accounting for 68% of the surveyed respondents conducted by Salt Labs.

Most common bot attacks on APIs
Bots are evolving rapidly and becoming more sophisticated than ever. The bots we are talking about today are no longer the simple crawlers that are simply executed from automation programs, nor the bots that make use of headless browsers and distribute larger scale attacks. The bots we are looking at are sophisticated ones that can simulate human-like interactions, such as mouse movements and they sometimes look like browsers themselves to bypass client side protections.
In order to notice API bot threats promptly, you could check the symptoms below (citing Redware):
- Single HTTP request (from a unique browser, session or a device)
- An increase in the rate of errors (e.g., HTTP status code 404, data validation failures, authorisation failures, etc.)
- Extremely high application usage from a single IP address or API token
- A sudden uptick in API usage from large, distributed IP addresses
- A high ratio of GET/POST to HEAD requests for a user/session/IP address/API token compared to legitimate users.
Compared with other bot attacks, attacks aiming APIs are harder to detect, but one thing we've already known is that malicious bots are the main tool for API attacks.
How to Make APIs Safe from Bot Attacks?
One of the advantages of bot attacks is that they are highly automated. There are three shortcuts that are often taken by attackers in order to make their attacks more efficient and effective in avoiding detection.
- Cybercriminals are becoming increasingly reliant on automated tools to execute bot attacks. They program specific commands and scripts targeting different events, such as login, online ordering, etc, to automate definite tasks on the Internet nonstop, day and night.
- Bad actors got loads of credential information to execute bot attacks and online fraud, like account takeover, denial of inventory, etc. Data breaches have become a regular thing in news. Cyber attackers sell stolen information for profit. The data that usually contains personal information, email address, phone number, password, and credit card information, etc., will spread among cybercriminals and fraudsters and be a great help to their bot attacks.
- Cloud control and group control allow bad actors to have access to hundreds and thousands of mobile devices via one group control platform. This feature helps them pass most bot detection schemes.

To secure APIs from bad bots, GeeTest views this issue from two aspects.
- Reduce bots efficiency
As a crucial advantage of bot attacks is that they are highly automated, in terms of their behavior (automated attacks), identities (countless credentials), and devices (cloud and group control platform), reducing the efficiency of their automation becomes the right path for security vendors.
- Increase attacker's cost
As long as efficiency is reduced (in terms of behavior, identise and devices), bad actors have to invest more in automated tools and buy more credential data and devices, which undoubtedly rise their cost of bot attacks. When the gap between cost and profit is lower than they expected, profit-happy cybercriminals will stop and turn around to another way, and defenders will cycle the process to curb attackers in another way.
The confrontation between attacker and defender is not simply about one side defeating the other, but a sustainable game in which one keeps trying to outsmart the other.
Solution for API Bot Attacks
Based on GeeTest's data, the attacks aiming APIs have one thing in common: massive repetitions and operations. Think about account takeover, scalping, denial of inventory, and so on. They are all automated attacks . In other words, they enjoy high efficiency in taking action by mimicking human behavior.
To help enterprises stop this kind of bot attacks, GeeTest released CAPTCHA v4 - Adaptive CAPTCHA, to tremendously reduce the efficiency of bots' actions.
Unlike legacy CAPTCHAs that detect bot activities simply based on limited parameters, such as image/text recognition (which can no longer stop sophisticated bot). To stop AI-powered bots who are getting better at understanding human interaction and can even mimic human behavior, security vendors should give attackers a taste of their own medicine.
GeeTest CAPTCHA v4 - Adaptive CAPTCHA provides a more intelligent, accurate and user-friendly replacement for legacy CAPTCHA systems. It uses a series of AI algorithms to detect malicious bots from more comprehensive dimensions than others.
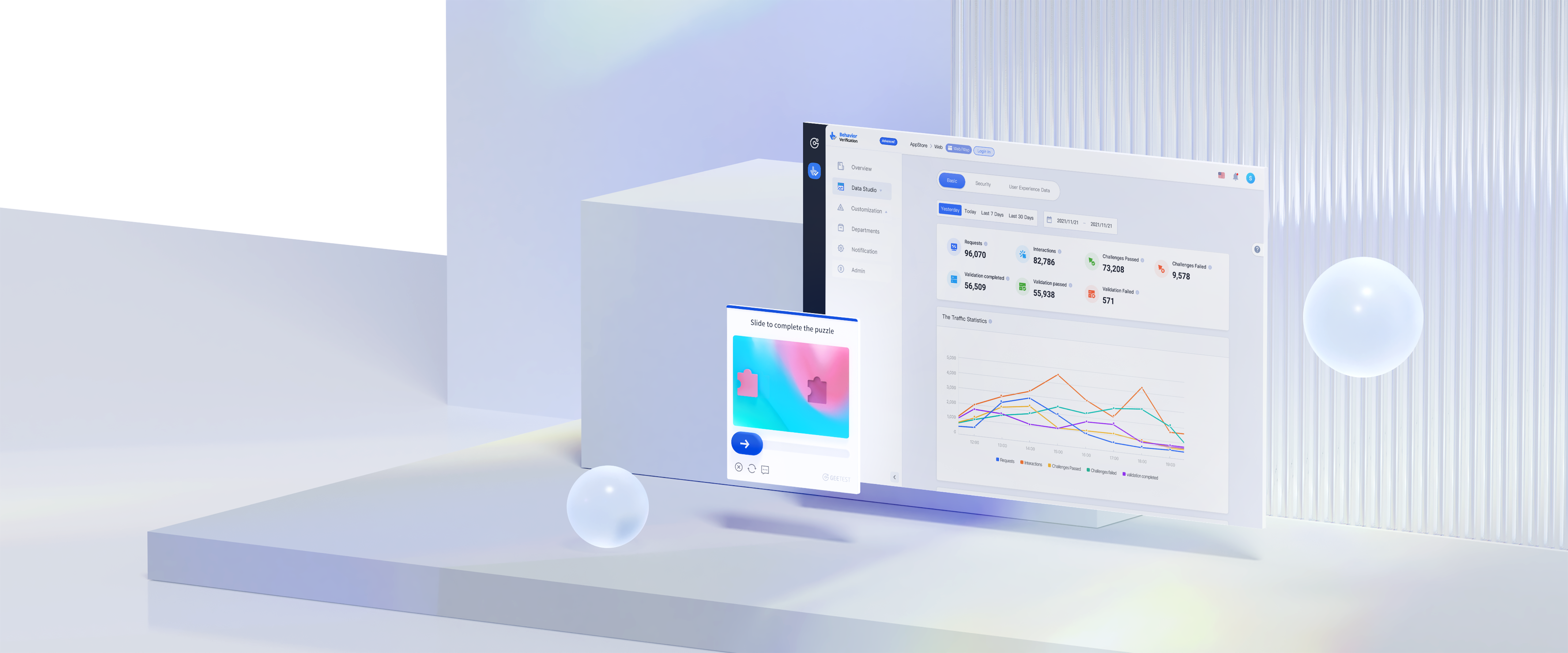
One fundamental feature of GeeTest CAPTCHA v4 that makes it distinct from other CAPTCHA systems is modularization.
The common workflow of a CAPTCHA looks like this.
- Client requests verification and CAPTCHA begins to detect risk in the background.
- Get CAPTCHA answers and user interaction data via CAPTCHA challenges.
- CAPTCHA service returns collected data to the client's side.
GeeTest CAPTCHA v4 makes every step an independent module and allows clients to decide how to use the modules to best fit their business and current risk control systems. In this way, companies can flexibly use the different modules of GeeTest CAPTCHA v4 to address their risk control needs in different scenarios and at different stages of development. The modular design of GeeTest CAPTCHA v4 provides the most suitable solution for specific requirements.
Here are three examples.
- When companies focus on a smooth user experience and do not want CAPTCHA to pop up and disturb users, they can use CAPTCHA v4 risk detection module to detect suspicious behaviour without popping up any CAPTCHA questions and return the risk data to enterprises, for their further analysis and actions.
- When an enterprise has its own risk control system and has the ability to analyse suspicious behaviour, it can use CAPTCHA challenge module of GeeTest CAPTCHA v4 to collect the user's response and make decisions through their own risk control system.
- When enterprises wish to supplement the capabilities of their own risk control system, they can use the risk analysis module of GeeTest CAPTCHA v4 to assist their own risk control system.
Register to try GeeTest CAPTCHA v4 free version here

Final Thoughts
Apart from CAPTCHA, there are actually a lot technologies enterprises can use to protect their APIs. Such as WAF, API gateway, cloud based service, dedicated bot management, and so on.
To choose a security tool or solution, enterprises should take these into consideration:
- Security capability
- Convenience
- Service stability
- User experience
API bot attacks continue to increase and the methods of bot attacks are evolving fast. Protecting API security requires agile tools and dynamically evolving solutions that can spot and stop API attacks before they happen.
One way we recommend is to adopt a tool or system that can handle real time detection and mitigation without interrupting users' experience.
GeeTest
GeeTest
Subscribe to our newsletter